9. Password Attack Methods
Password Attack Methods
Password attack methods refer to various techniques used by malicious individuals to gain unauthorized access to user accounts or systems by exploiting weak or vulnerable passwords. These attacks aim to bypass authentication mechanisms and compromise user privacy or system security. Here are four common password attack methods:
Brute Force Attacks: In this method, an attacker systematically tries all possible combinations of characters until the correct password is discovered. Brute force attacks can be time-consuming, especially for complex passwords. However, they can be successful against weak passwords or when the attacker has access to powerful computational resources.
Dictionary Attacks: This method involves using a pre-existing list of commonly used passwords or words from a dictionary to guess the password. Attackers automate the process by using software that rapidly tries different combinations. Dictionary attacks are effective against users who choose easily guessable passwords, such as "password" or "123456."
Phishing Attacks: Phishing attacks rely on tricking users into revealing their passwords willingly. Attackers often create fake login pages or send deceptive emails pretending to be legitimate organizations. If users unknowingly enter their passwords on these fraudulent platforms, the attackers gain access to their accounts. Phishing attacks exploit human vulnerabilities rather than technical weaknesses.
Rainbow Table Attacks: Rainbow tables are precomputed tables that map password hashes to their corresponding plaintext passwords. In this attack, an attacker compares the hash values of stolen password databases with entries in a rainbow table to find the original passwords. This method is effective against unsalted password hashes and can rapidly reveal passwords if the corresponding hash is present in the table.
To protect against these password attack methods, it is crucial to follow best practices such as using strong, unique passwords for each account, enabling multi-factor authentication, and staying vigilant against phishing attempts. Additionally, organizations should implement measures like account lockouts, rate limiting, and password complexity requirements to enhance password security.
-
 1:15:28
1:15:28
Precision Rifle Network
1 day agoGuns & Grub S2E7
30.7K6 -
 2:23:00
2:23:00
Donald Trump Jr.
12 hours agoLIVE WITH RUSSELL BRAND | TRIGGERED Ep.143
154K204 -
 1:19:17
1:19:17
Glenn Greenwald
8 hours agoSteve Bannon's Contempt Charges Reveal Historic Double Standard; Interview with RFK Jr.'s Running Mate Nicole Shanahan on the 2024 Election and More | SYSTEM UPDATE #278
74.7K166 -
 1:02:52
1:02:52
The Late Kick with Josh Pate
9 hours agoLate Kick Live Ep 519: CFB’s Biggest ?s | Hall-Of-Fame Broken | Deion Expectations | Bold Predictions
27.3K2 -
 59:54
59:54
The StoneZONE with Roger Stone
8 hours agoThe 2024 GOP National Platform Will Be Donald Trump's - w/ Ed Martin | The StoneZONE w/ Roger Stone
34K1 -
 LIVE
LIVE
Right Side Broadcasting Network
3 days agoLIVE REPLAY: "Chase the Vote" Town Hall With President Donald J. Trump - 6/6/2024
3,225 watching -
 1:55:36
1:55:36
The Quartering
10 hours agoSteven Bannon To Prison, Biden Deuces His Pants, Wokest Star Wars Disaster & More
70K34 -
 2:03:41
2:03:41
Quite Frankly
11 hours ago"The Boyd Flu, The Unjected, D-Day, and Patton" ft Shelby Hosana 6/6/24
39.3K22 -
 1:07:10
1:07:10
TheMonicaCrowleyPodcast
11 hours agoThe Monica Crowley Podcast: The War Within
21.5K6 -
 1:19:36
1:19:36
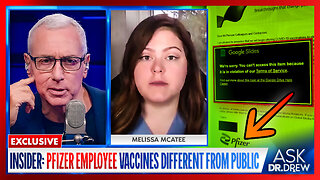
Dr. Drew
12 hours agoExclusive: Pfizer Insider Says Employees Received Different mRNA Shots Than Public, Was Fired After Voicing Her Concerns w/ Melissa McAtee & David 'Nino" Rodriguez – Ask Dr. Drew
57.9K47